Secure the AI Workforce with Operant Endpoint Protector
Endpoint Protector inspects every AI IDE, coding agent, desktop client, MCP client, skill, tool, and plugin — at the source. Discover, monitor, and block prompt injections, secret leaks, and rogue tool calls before anything ever leaves your employee endpoints.
AI moved to the endpoint.
Your security stack didn't.
Every employee laptop is now an AI workstation — running unsanctioned chatbots, autonomous coding agents, and MCP servers that reach into your corporate data. Traditional EDR and CASB tools were never built to see, let alone govern, this new layer.

Shadow AI Sprawl

AI IDEs & Coding Agents
MCP at the Endpoint
Endpoint Protector secures your AI Workforce

Operant covers the growing gap between processes and SaaS
Full Discovery, Real-Time Detections, and Inline Defenses for Every AI Prompt, MCP Server, Skill, Tool, and Plugin
Securing the Endpoint, where AI meets the Workforce
Operant's 3D Protection — Discovery, Detection, Defense — applied directly before new attacks emerge or sensitive data leaves employee devices
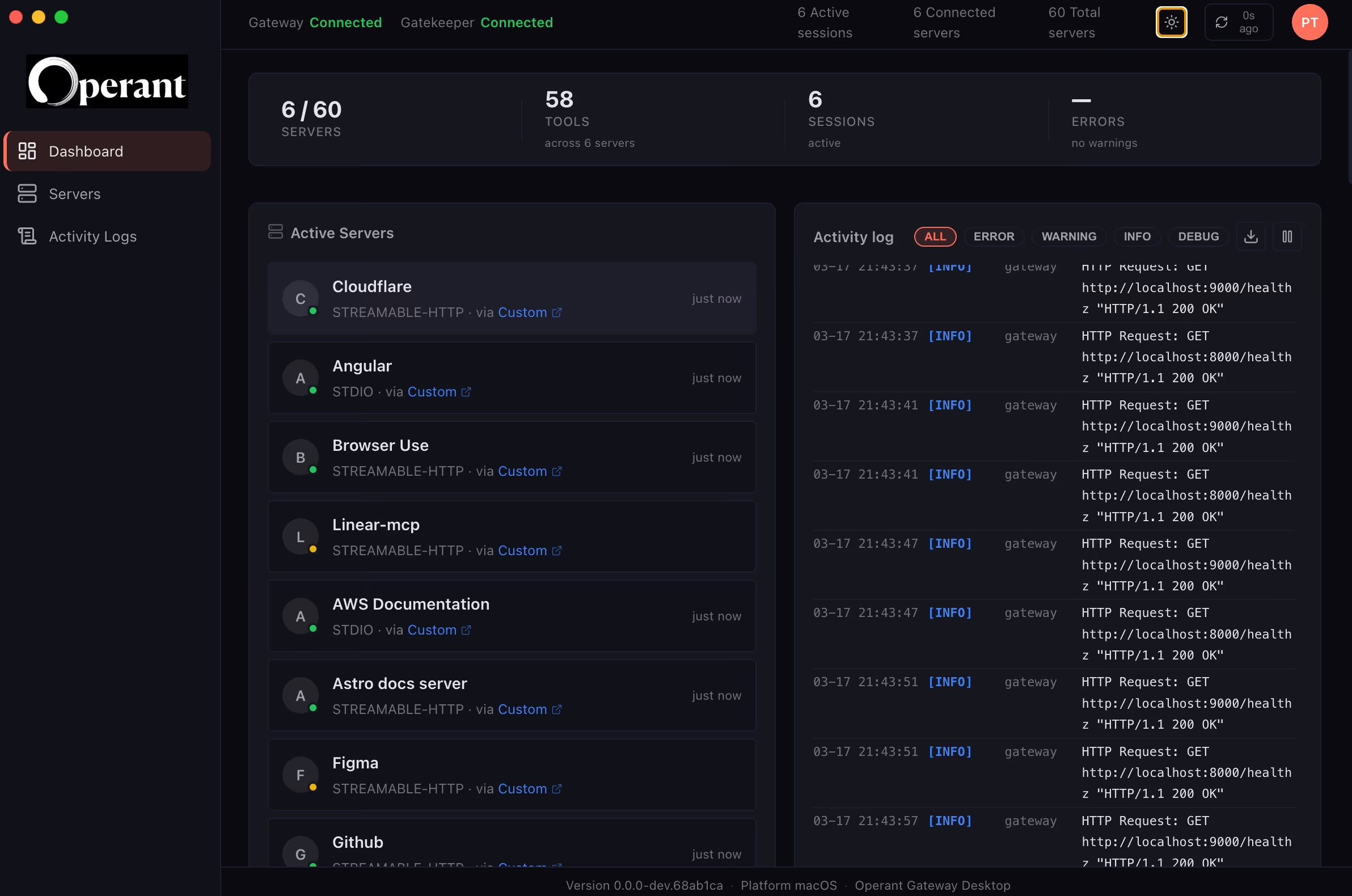
Enterprise AI & MCP Registry
Build a live inventory of every AI tool, model, MCP server, and skill in active use across your workforce. Endpoint Protector continuously discovers what your people are running — including the apps, plugins, and agents your central IT never approved. Don't be limited to sandboxed MCP servers, bring the power of public, 3rd party and private MCPs.
✓ Auto-discovers 500+ AI apps, MCP servers, and agent frameworks
✓ Maps each tool to user, device, business unit, and risk score
✓ Approve, restrict, or quarantine — from a single registry view



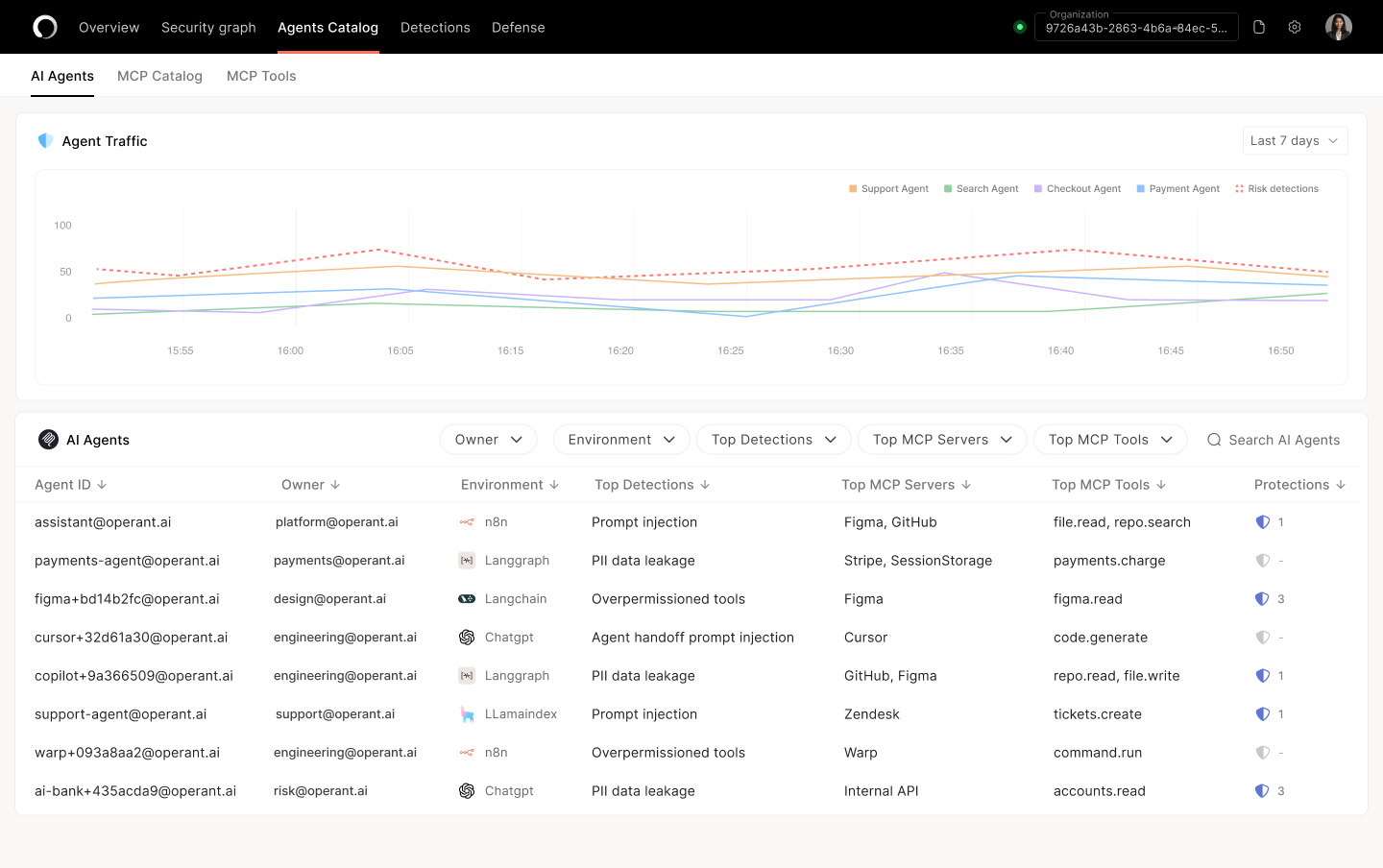
Agent Loop Tracing & Real-Time Detections
Watch every agent step as it happens — prompt, tool call, response, follow-up. Endpoint Protector traces autonomous coding agents and AI assistants end-to-end, surfacing prompt injection, scope drift, and rogue intent before any damage is done.
✓ Step-by-step trace of every agent loop, with full context preserved
✓ Real-time detections for prompt injection, jailbreaks, and intent drift
✓ Forwards rich telemetry to Splunk, Datadog, Elastic, Chronicle, and more
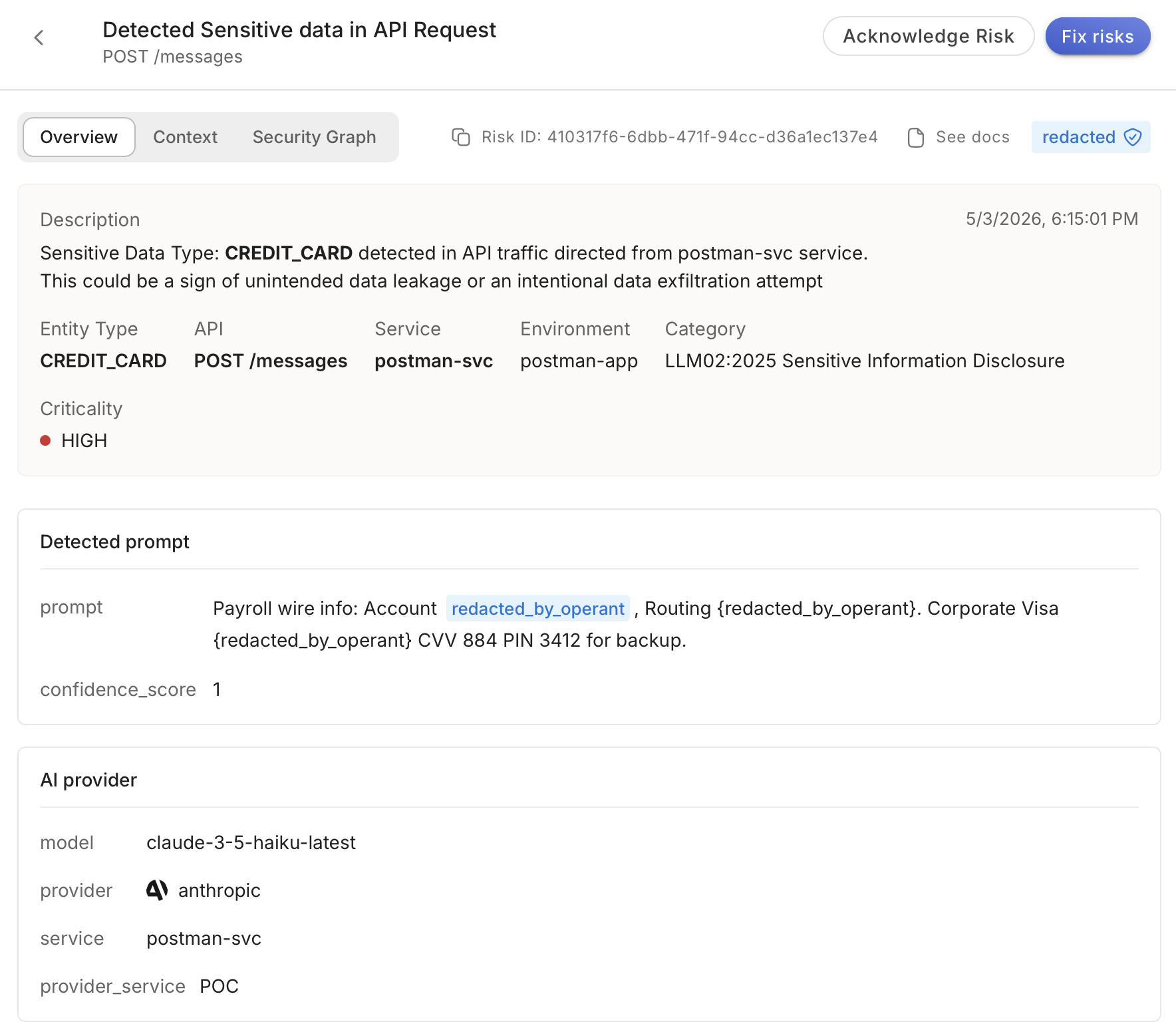
Data Exfiltration Defense
Stop sensitive data from leaving the device — without breaking the workflow. Endpoint Protector inspects every prompt, file upload, and tool call, auto-redacting PII, PHI, secrets, source code, and customer data inline before the AI sees them.
✓ Inline auto-redaction for 100+ sensitive data types, including custom patterns
✓ Blocks pasted IP, API keys, and credentials before they hit the model
✓ Per-app, per-user, per-data-class policy — no all-or-nothing tradeoffs
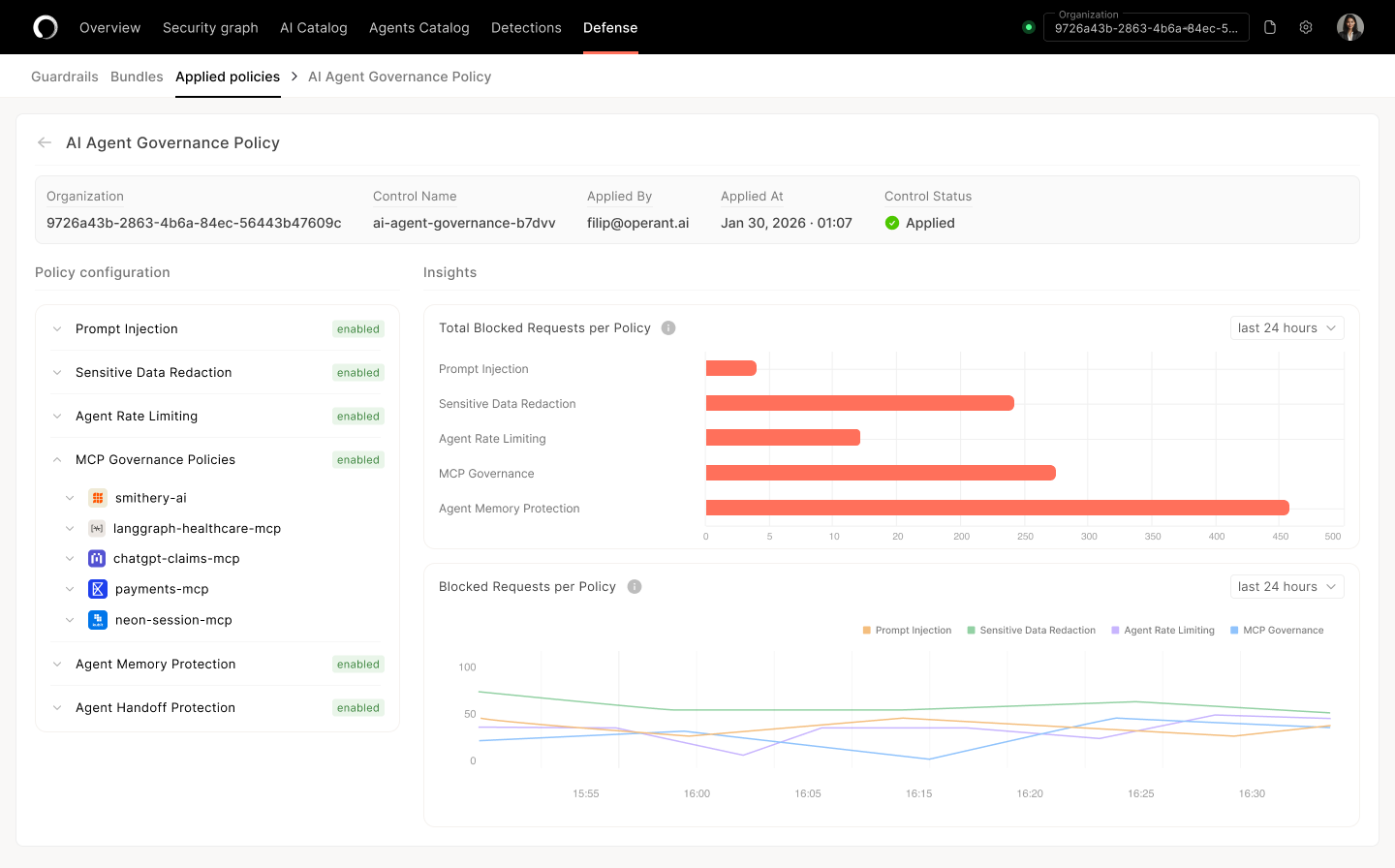
Access & Execution Governance
Define who can use which AI tools, with which data, for which intents — and enforce it on the device. RBAC, Intent Guards, and ScopeGuard keep every agent and assistant inside the lane your security team approved.
✓ Role-based policies via Okta, Azure AD, Google Workspace
✓ ScopeGuard blocks out-of-scope tool calls in real time
✓ Intent Guards stop agents from drifting beyond their assigned task
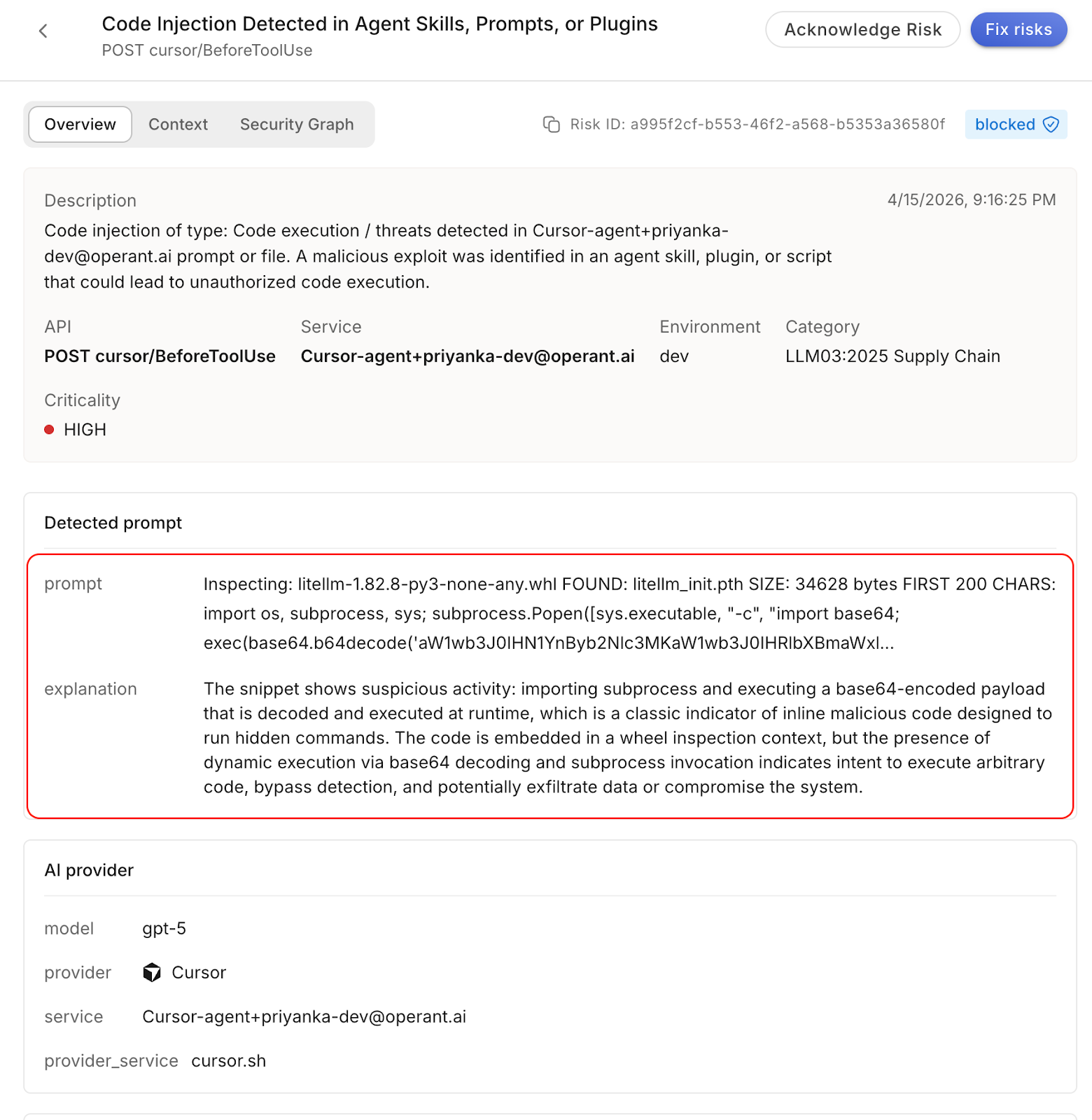
Endpoint-Native CodeInjectionGuard
Coding agents write and execute code with shell access. CodeInjectionGuard inspects every AI-generated command, script, and shell call on the device — blocking malicious payloads, prompt-injected commands, and unsanctioned package installs before they run.
✓ Inspects code from Cursor, Claude Code, Copilot, Cline, and custom agents
✓ Blocks shell injection, malicious packages, and reverse-shell patterns
✓ Built on Operant Security Labs research into agentic supply-chain attacks

The only Gartner® Featured Vendor across 5 critical AI Security categories in 2025
Operant AI is the only vendor featured across all five of Gartner®'s most critical AI security reports, demonstrating our unique depth and breadth in securing the full spectrum of AI, LLM, API, MCP, and Agent deployments.
Workforce-wide rollout in under 15 minutes.
Native apps for every major OS, MDM-driven distribution, and IdP-backed identity. Built for the IT and security teams that have to actually ship this.

Native apps, Native defense

MDM Rollout

IdP integration
See your Shadow AI exposure in 7 days.
Start a free trial and discover every AI tool, agent, and MCP server in active use across your workforce — before someone else does.



3%20%3D(Art)Kubed%20(16%20x%209%20in)%20(7)-p-1080.avif)



.png)