Introducing Endpoint Protector: Purpose Built Security for the AI Workforce

Evaluate your spending
Imperdiet faucibus ornare quis mus lorem a amet. Pulvinar diam lacinia diam semper ac dignissim tellus dolor purus in nibh pellentesque. Nisl luctus amet in ut ultricies orci faucibus sed euismod suspendisse cum eu massa. Facilisis suspendisse at morbi ut faucibus eget lacus quam nulla vel vestibulum sit vehicula. Nisi nullam sit viverra vitae. Sed consequat semper leo enim nunc.
- Lorem ipsum dolor sit amet consectetur lacus scelerisque sem arcu
- Mauris aliquet faucibus iaculis dui vitae ullamco
- Posuere enim mi pharetra neque proin dic elementum purus
- Eget at suscipit et diam cum. Mi egestas curabitur diam elit
Lower energy costs
Lacus sit dui posuere bibendum aliquet tempus. Amet pellentesque augue non lacus. Arcu tempor lectus elit ullamcorper nunc. Proin euismod ac pellentesque nec id convallis pellentesque semper. Convallis curabitur quam scelerisque cursus pharetra. Nam duis sagittis interdum odio nulla interdum aliquam at. Et varius tempor risus facilisi auctor malesuada diam. Sit viverra enim maecenas mi. Id augue non proin lectus consectetur odio consequat id vestibulum. Ipsum amet neque id augue cras auctor velit eget. Quisque scelerisque sit elit iaculis a.

Have a plan for retirement
Amet pellentesque augue non lacus. Arcu tempor lectus elit ullamcorper nunc. Proin euismod ac pellentesque nec id convallis pellentesque semper. Convallis curabitur quam scelerisque cursus pharetra. Nam duis sagittis interdum odio nulla interdum aliquam at. Et varius tempor risus facilisi auctor malesuada diam. Sit viverra enim maecenas mi. Id augue non proin lectus consectetur odio consequat id vestibulum. Ipsum amet neque id augue cras auctor velit eget.
Plan vacations and meals ahead of time
Massa dui enim fermentum nunc purus viverra suspendisse risus tincidunt pulvinar a aliquam pharetra habitasse ullamcorper sed et egestas imperdiet nisi ultrices eget id. Mi non sed dictumst elementum varius lacus scelerisque et pellentesque at enim et leo. Tortor etiam amet tellus aliquet nunc eros ultrices nunc a ipsum orci integer ipsum a mus. Orci est tellus diam nec faucibus. Sociis pellentesque velit eget convallis pretium morbi vel.
- Lorem ipsum dolor sit amet consectetur vel mi porttitor elementum
- Mauris aliquet faucibus iaculis dui vitae ullamco
- Posuere enim mi pharetra neque proin dic interdum id risus laoreet
- Amet blandit at sit id malesuada ut arcu molestie morbi
Sign up for reward programs
Eget aliquam vivamus congue nam quam dui in. Condimentum proin eu urna eget pellentesque tortor. Gravida pellentesque dignissim nisi mollis magna venenatis adipiscing natoque urna tincidunt eleifend id. Sociis arcu viverra velit ut quam libero ultricies facilisis duis. Montes suscipit ut suscipit quam erat nunc mauris nunc enim. Vel et morbi ornare ullamcorper imperdiet.
The endpoint is now an AI workstation.
Three years ago, the riskiest application on a corporate laptop was a browser. Today it's a coding agent that can read your filesystem, execute shell commands, install packages, call internal APIs, and ship code to production — often in a single autonomous loop. Next to it sits a chat window where employees paste customer data, source code, and credentials into models running on someone else's infrastructure. And underneath both, a quietly growing layer of MCP clients connecting to servers nobody on the security team has ever audited.
This isn't a forecast. It's already the average enterprise endpoint. And it represents a category of risk that traditional endpoint security was never designed to address.
EDR sees processes. It tells you a binary executed, a network connection opened, a file was written. It doesn't know what was in the prompt, which tool the agent called, or whether a malicious MCP server just talked the agent into reading ~/.aws/credentials.
CASB sees SaaS traffic. It tells you which sanctioned apps employees use and applies coarse policy at the network edge. It doesn't see the local AI assistant, the IDE-resident agent, or the MCP call that never touches a SaaS proxy because it's brokered locally on the device.
Both tools remain essential. But neither was built for an endpoint where the most sensitive activity is conversational, autonomous, and shaped like language.
"We talk to security leaders every week who can name the AI tools they've approved — and have no idea what's actually running on their employees' machines. Endpoint Protector is the layer that closes that gap."
Three threats hiding in plain sight.
When we talked to design partners about what they were actually losing sleep over, three patterns came back repeatedly. None of them are theoretical.
Shadow AI sprawl
The average enterprise has dozens to hundreds of unsanctioned AI tools in active daily use — chatbots, summarizers, transcribers, code assistants. Sensitive data flows into them constantly, often by employees with the best intentions trying to work faster. Security teams can't govern what they can't see, and existing discovery tools either miss the local apps entirely or surface them weeks after the data already left.
AI IDEs and coding agents
Cursor, Claude Code, Copilot, Cline, and a growing list of agentic coding tools run loops on developer machines that include shell execution, file system access, and dependency installation. A single prompt-injected README file in an open-source repo can talk one of these agents into shipping malicious code — or quietly exfiltrating environment variables. We've seen this pattern in Operant Labs research, and the attack surface is expanding faster than any single team can keep up with.
MCP at the endpoint
MCP — Model Context Protocol — is the new connective tissue between AI agents and the tools they use. Most MCP clients live on the endpoint, brokering calls to servers your security team has never reviewed. Our research team's Shadow Escape work documented how a malicious MCP server can override agent intent, hijack tool calls, and exfiltrate data — all within an interaction that looks completely normal from the network's point of view.
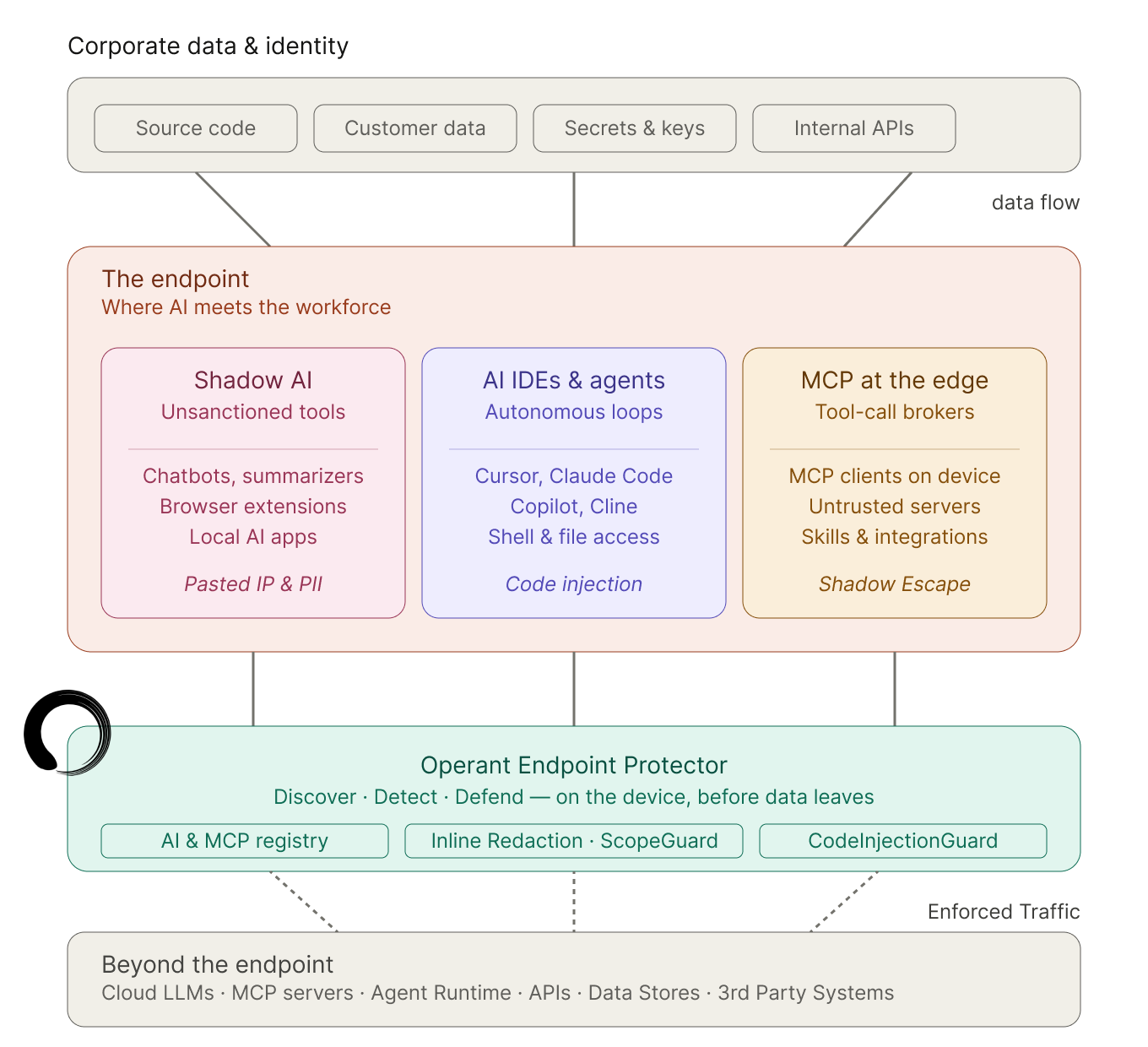
What we built.
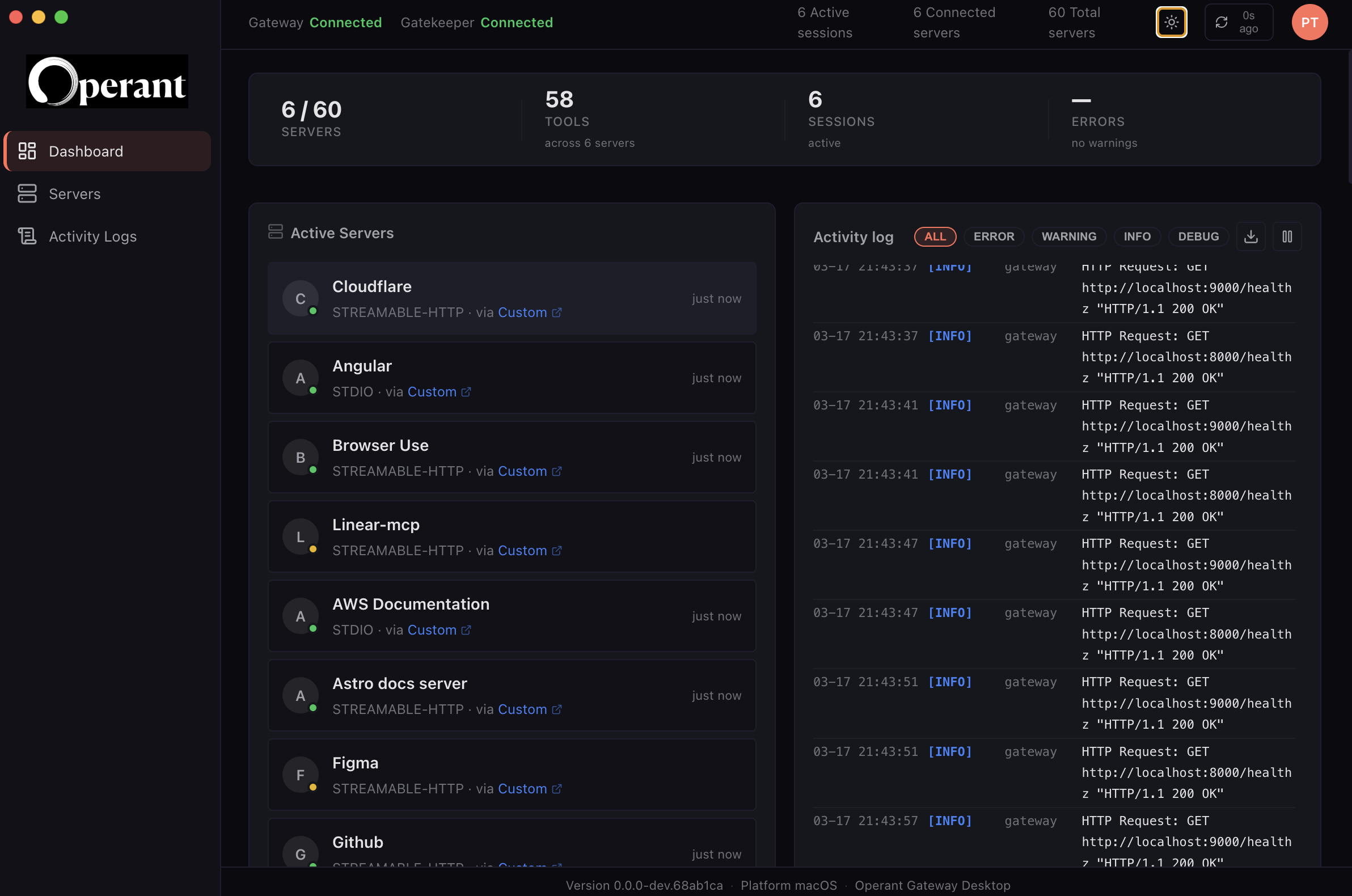
Endpoint Protector applies Operant's 3D Protection methodology — Discovery, Detection, Defense — directly on the device. It runs as a lightweight native app on macOS, Windows, and Linux, integrates with the IdP and MDM tools your IT team already uses, and ships with five core capabilities:
Enterprise AI & MCP Registry
A live inventory of every AI tool, model, MCP server, and skill in use across the workforce — mapped to user, device, business unit, and risk score. Approve, restrict, or quarantine from a single view.
Agent Loop Tracing & Real-Time Detections
Step-by-step trace of every agent loop with full context preserved. Real-time detections for prompt injection, jailbreaks, and intent drift. Telemetry exports natively to Splunk, Datadog, Elastic, and Chronicle.
Data Exfiltration Defense
Inline auto-redaction for 80+ sensitive data types — PII, PHI, source code, secrets, customer records — applied to every prompt, file upload, and tool call before the AI ever sees them.
Access & Execution Governance
Role-based policies via Okta, Azure AD, and Google Workspace. ScopeGuard™ blocks out-of-scope tool calls. Intent Guards stop agents from drifting beyond their assigned task — enforced on the device, not just at a gateway.
Endpoint-Native CodeInjectionGuard™
Inspects every AI-generated command, script, and shell call on the device. Blocks shell injection, malicious packages, and reverse-shell patterns before they execute — built directly on Operant Labs research into agentic supply-chain attacks.
Built to ship in your environment.
We built Endpoint Protector with a specific reality in mind: the security team approves it, but the IT team has to actually deploy it across thousands of laptops without breaking workflows or burning a quarter of help desk capacity.
Endpoint Protector is a native, lightweight app — no kernel extensions required. It distributes through Jamf, Intune, Workspace ONE, and Kandji with one-click rollout. Identity flows from Okta, Azure AD, or Google Workspace, so RBAC policies inherit directly from the directory you already trust. And for regulated industries and enterprises with high compliance requirements, it ships with private-mode and hybrid deployment options.
Audit logs are exhaustive and exportable, with mappings to SOC 2, HIPAA, NIST AI RMF, and OWASP LLM Top 10. The compliance backbone is built in, not bolted on.
From endpoint to cloud.
Endpoint Protector closes the gap at the workforce layer. But endpoint security alone isn't an AI security strategy. The same agent that runs in a developer IDE today ships to production tomorrow. The same data path that risks exposure on a laptop runs through services in the cluster.
That's why Endpoint Protector ships as part of the broader Operant platform. Agent Protector extends the same identity, intent, and scope controls to agents running in production — so the security model that started on the developer's laptop carries through to where the agent actually does its work. The rest of the platform extends that same coverage across every other layer where AI lives in your environment: applications, APIs, infrastructure, and the runtime that connects them.
One platform, one policy plane, one audit trail — from the laptop to the cluster. That's the difference between adding another point tool and actually solving for AI risk end to end.
Get started today.
Endpoint Protector is available today. Customers can start with a 7-day free trial — full feature access, no credit card required. Most teams have a complete Shadow AI inventory within the first 24 hours. Enterprises can get started today, whether it's for 10+ or 1,000+ endpoints. Our team will walk you through deployment, IdP configuration, and the first set of policies — typically a one-week engagement to full scale deployment.



3%20%3D(Art)Kubed%20(16%20x%209%20in)%20(7)-p-1080.avif)




.png)

.png)