Security at the Speed of AI

Evaluate your spending
Imperdiet faucibus ornare quis mus lorem a amet. Pulvinar diam lacinia diam semper ac dignissim tellus dolor purus in nibh pellentesque. Nisl luctus amet in ut ultricies orci faucibus sed euismod suspendisse cum eu massa. Facilisis suspendisse at morbi ut faucibus eget lacus quam nulla vel vestibulum sit vehicula. Nisi nullam sit viverra vitae. Sed consequat semper leo enim nunc.
- Lorem ipsum dolor sit amet consectetur lacus scelerisque sem arcu
- Mauris aliquet faucibus iaculis dui vitae ullamco
- Posuere enim mi pharetra neque proin dic elementum purus
- Eget at suscipit et diam cum. Mi egestas curabitur diam elit
Lower energy costs
Lacus sit dui posuere bibendum aliquet tempus. Amet pellentesque augue non lacus. Arcu tempor lectus elit ullamcorper nunc. Proin euismod ac pellentesque nec id convallis pellentesque semper. Convallis curabitur quam scelerisque cursus pharetra. Nam duis sagittis interdum odio nulla interdum aliquam at. Et varius tempor risus facilisi auctor malesuada diam. Sit viverra enim maecenas mi. Id augue non proin lectus consectetur odio consequat id vestibulum. Ipsum amet neque id augue cras auctor velit eget. Quisque scelerisque sit elit iaculis a.

Have a plan for retirement
Amet pellentesque augue non lacus. Arcu tempor lectus elit ullamcorper nunc. Proin euismod ac pellentesque nec id convallis pellentesque semper. Convallis curabitur quam scelerisque cursus pharetra. Nam duis sagittis interdum odio nulla interdum aliquam at. Et varius tempor risus facilisi auctor malesuada diam. Sit viverra enim maecenas mi. Id augue non proin lectus consectetur odio consequat id vestibulum. Ipsum amet neque id augue cras auctor velit eget.
Plan vacations and meals ahead of time
Massa dui enim fermentum nunc purus viverra suspendisse risus tincidunt pulvinar a aliquam pharetra habitasse ullamcorper sed et egestas imperdiet nisi ultrices eget id. Mi non sed dictumst elementum varius lacus scelerisque et pellentesque at enim et leo. Tortor etiam amet tellus aliquet nunc eros ultrices nunc a ipsum orci integer ipsum a mus. Orci est tellus diam nec faucibus. Sociis pellentesque velit eget convallis pretium morbi vel.
- Lorem ipsum dolor sit amet consectetur vel mi porttitor elementum
- Mauris aliquet faucibus iaculis dui vitae ullamco
- Posuere enim mi pharetra neque proin dic interdum id risus laoreet
- Amet blandit at sit id malesuada ut arcu molestie morbi
Sign up for reward programs
Eget aliquam vivamus congue nam quam dui in. Condimentum proin eu urna eget pellentesque tortor. Gravida pellentesque dignissim nisi mollis magna venenatis adipiscing natoque urna tincidunt eleifend id. Sociis arcu viverra velit ut quam libero ultricies facilisis duis. Montes suscipit ut suscipit quam erat nunc mauris nunc enim. Vel et morbi ornare ullamcorper imperdiet.
The energy at NVIDIA's GTC conference this year was unmistakable. Developers, researchers, and enterprise leaders converged around a shared truth: the foundational AI Infra is fundamentally transforming to keep pace and scale for the Agentic Era. From real-time inference to multi-agent orchestration, GPUs and the fast inference engines are the beating heart of every breakthrough on the show floor.
But amid the excitement, a quieter and far more urgent conversation was happening on the sidelines: if AI runs at GPU speed, security has to as well. AI security that slows things down isn't security — it's a bottleneck. And in a world where agentic AI systems are making decisions in milliseconds, a slow and traditional security layer is worse than useless. It's a liability.
At Operant, we've built our AI detection and defense platform around exactly this principle — and we're doing it on two fronts that are converging fast: the laptop endpoint and the cloud, powering enterprises to bring powerful security capabilities in “private-mode”.
Security That Stays Within Your Sovereign Compute
For organizations with strict data residency requirements or a preference for sovereign compute, Operant's deployment model is worth noting. Detection and defense runs entirely within your own environment — your VPC, on-premises infrastructure, or hybrid cloud. Operant never pulls your data into our cloud to analyze it.
This matters to customers who need their security tooling to operate within a defined sovereign compute boundary, whether that's driven by regulation, internal policy, or simply a preference for keeping sensitive AI workloads on infrastructure they control. Many AI security vendors require your traffic or telemetry to egress to their cloud as part of how their product works. Operant doesn't — the detections and defenses run where your data already lives.
OpenClaw, the Newest Attack Surface for Endpoints
Projects like OpenClaw are genuinely transformative. The ability to automate complex tasks, chain actions across apps, and let an AI agent operate autonomously on your behalf — it's a Pandora's box of productivity. It's also a Pandora's box of risk, and it's just the tip of the iceberg.
When an agentic system runs locally with access to files, browsers, email, and APIs, the laptop stops being a device that stores data. It becomes an autonomous actor. And autonomous actors can be manipulated.
The most uncomfortable truth about endpoint AI security is this: employees and consumers are not equipped to identify or stop these attacks — and it's not their fault. When an OpenClaw agent is running, its behavior looks identical whether it's working correctly, being overly aggressive, or executing instructions planted by a malicious actor. An employee watching their agent busily process emails and documents has no reliable way to distinguish productivity from exfiltration. Even an agent that's simply being too "helpful" — accessing more files than necessary, chaining more tool calls than intended — can cause a breach through nothing more than ambition.
Zero-click attacks make this worse by removing the human entirely. A malicious prompt injection buried in a document the agent summarizes or a webpage it browses can silently redirect its behavior without the user ever seeing anything unusual. By the time someone notices, the damage is done — if they notice at all.
Tool poisoning exploits the trust users place in their agent's tools. When a plugin or API integration is compromised, the agent doesn't malfunction — it follows its instructions faithfully, just the wrong ones. Across millions of OpenClaw users sharing the same tool ecosystem, one compromised integration becomes a coordinated, simultaneous, invisible attack at scale.
Data exfiltration finds its most efficient vehicle yet in an agent with broad local permissions — moving credentials, documents, and personal data at machine speed, with a footprint indistinguishable from normal activity.
With faster GPUs and inference horsepower coming to endpoints, the modern incarnations of OpenClaw will continue becoming very powerful. These agents operate in millisecond windows, and the attacks they enable execute in the same windows. Operant's Endpoint Protection can run GPU-accelerated detections, mitigating threats at the moment of execution — not after.
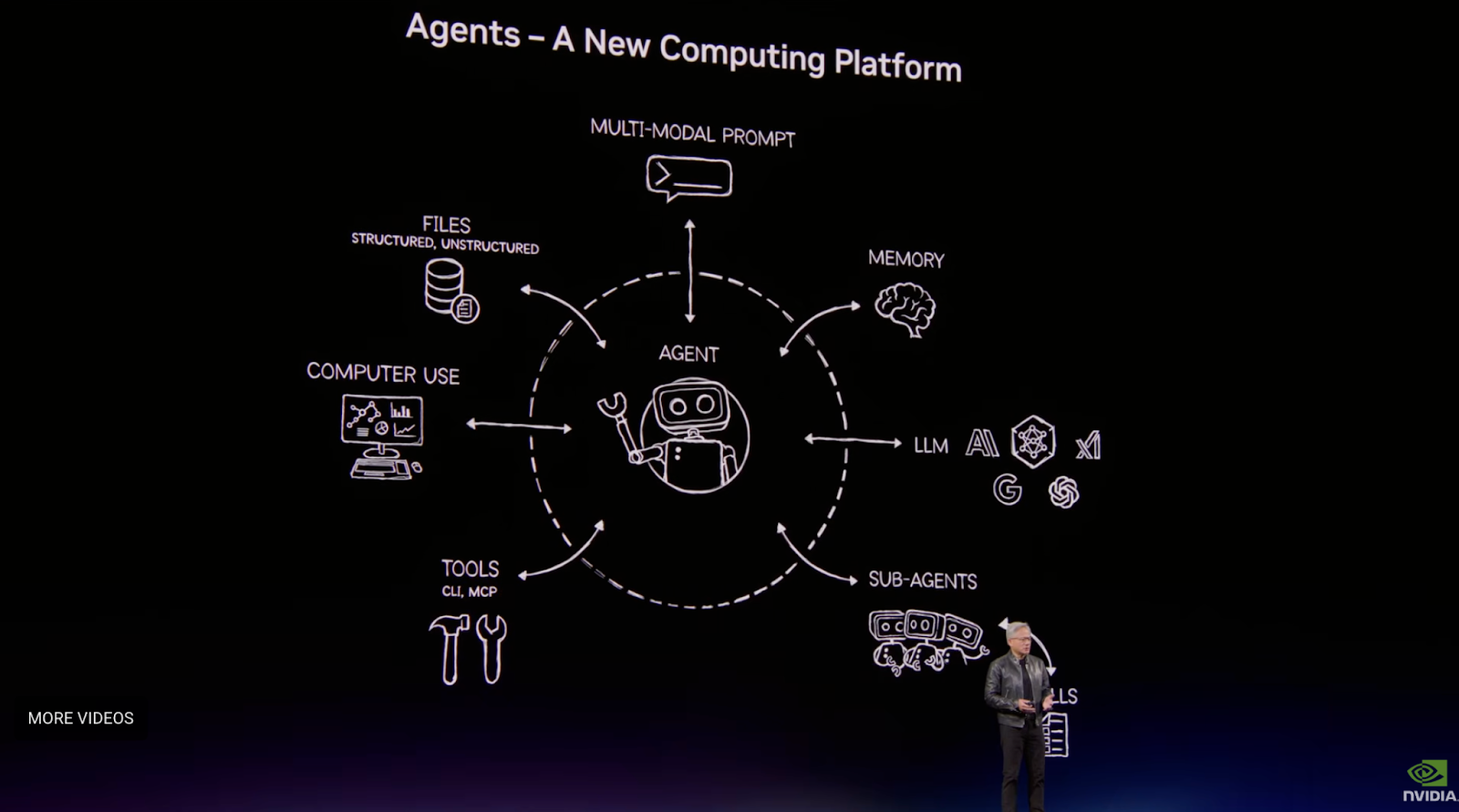
Agentic Cloud Is a Different Beast Entirely
If OpenClaw represents a new employee threat surface, platforms like LangChain, n8n, and CrewAI represent a different reckoning — one already deep inside enterprise infrastructure and scaling fast. The threat vectors rhyme, but the architecture and blast radius are orders of magnitude different.
The most important distinction is observability. When OpenClaw misbehaves on a laptop, there's likely a human in the loop who might notice. In cloud-based agentic pipelines, no one is watching — and by design, no one should need to. A LangChain pipeline ingesting thousands of documents per hour, a CrewAI system coordinating a crew of parallel specialized agents, an n8n workflow stitching together CRMs, databases, and APIs in sequence — these run autonomously because that's the entire value proposition. But it also means there's no human observation layer between a malicious instruction and its execution.
Prompt injection at pipeline scale is a different animal. A poisoned document in a LangChain RAG pipeline doesn't affect one user — it injects malicious instructions into every downstream step that processes its output. In a CrewAI system, corrupted context from one agent propagates through the entire crew via the same inter-agent messaging that makes the system work. One malicious input. Dozens of tainted outputs. No anomalous signatures, because the system is behaving exactly as designed.
Tool poisoning in the cloud has a supply chain dimension that doesn't exist on the endpoint. A compromised tool in a widely-deployed LangChain template doesn't affect one pipeline — it affects every organization that forked it. A poisoned n8n community node propagates silently into every workflow that uses it, executing its next attack the moment the next scheduled run fires.
Data exfiltration in cloud pipelines isn't bounded by what one user can access — it's bounded by what the pipeline can access. In enterprise deployments, that means production databases, customer records, financial systems, and the API credentials to reach all of them. A CrewAI system with one compromised agent can use normal inter-agent messaging to route stolen data through a step that looks, in every log, like a standard workflow action. An n8n workflow moving data between systems looks identical whether it's sending one copy or two.
All the celebrated hardware updates at GTC are going to power the next wave of AI Infra – powering the very demanding agentic workloads. But they introduce a challenge the endpoint doesn't have: concurrency. Hundreds of agent instances executing simultaneously across distributed infrastructure cannot be inspected by a CPU-bound security layer without creating gaps. It will always be behind. Operant's GPU-accelerated cloud detections run inline with the agent infrastructure, evaluating every tool call and every inter-agent message in parallel — not sampling, not post-hoc. Every action, every time.
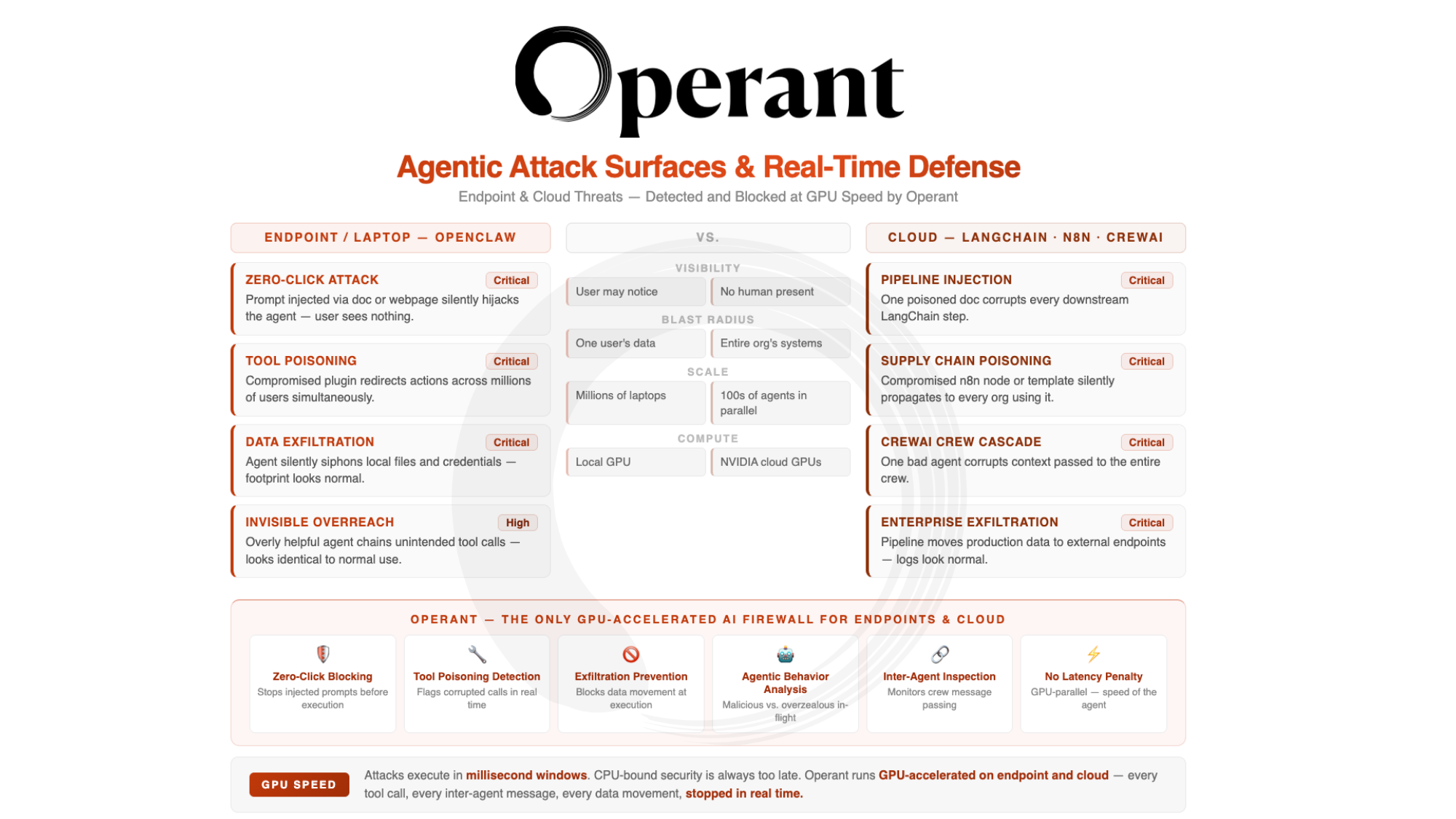
The AI-Layer Firewall built for this Agentic Era
The endpoint and cloud threats are related but distinct. OpenClaw puts an autonomous actor on every laptop, invisible to the person sitting in front of it. LangChain, CrewAI, and n8n put autonomous pipelines inside enterprise infrastructure, invisible to nearly everyone. Both attack surfaces are real. Both are moving fast. Both demand security that operates at the speed of the systems it protects.
Operant is the only solution on the market today that protects AI endpoints and cloud agentic infrastructure with a GPU-accelerated platform, including AI Gatekeeper, MCP Gateway, and Agent Protector — detecting and blocking zero-click attacks, tool poisoning, and data exfiltration in real time, without slowing down the workflows that make agentic AI valuable in the first place.
Because AI security has to run at the speed of AI. And now, finally, it does.
Operant is the AI security platform built for the agentic era — GPU-accelerated, real-time, and the fastest in the industry. Learn more at operant.ai.



3%20%3D(Art)Kubed%20(16%20x%209%20in)%20(7)-p-1080.avif)





.png)
